Email. Pah.
Blog
The latest tips & tricks from the ThreatPipes team.
Research | Announcements | Product
-
Crafting a Phishing Domain
Research January 21, 2020
-
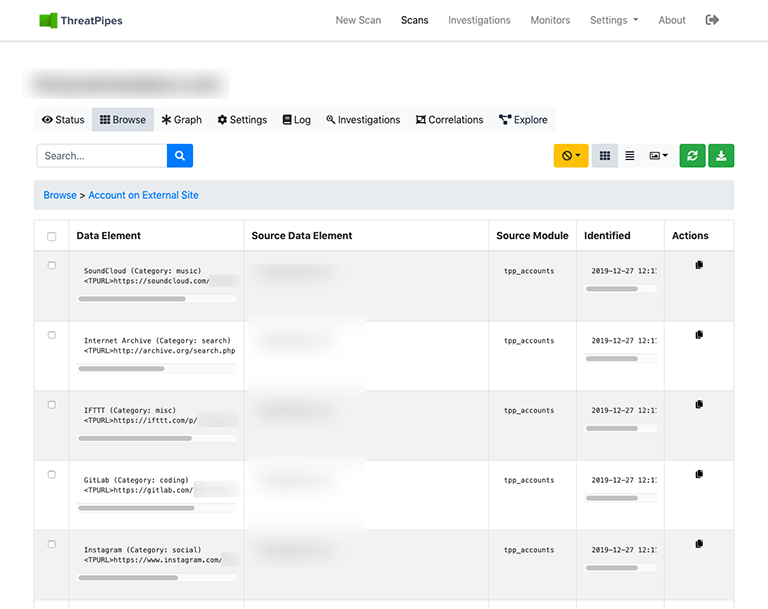
The danger of random LinkedIn connections
Research January 14, 2020
I have 6 LinkedIn accounts.
-
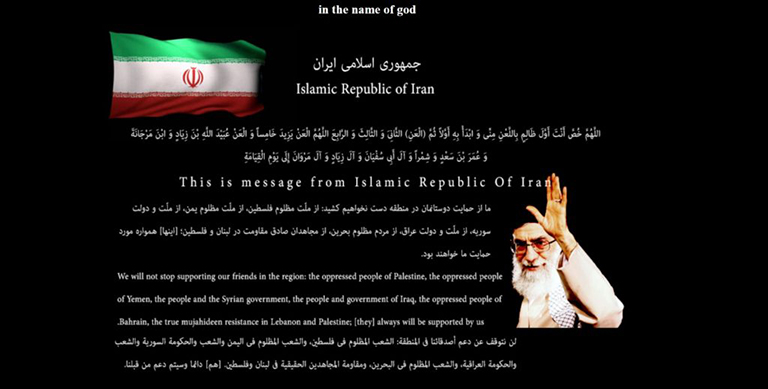
Hacked By Iran Cyber Security Group HackerS
Research January 07, 2020
Just kidding.
-
Don't F*** with ThreatPipes
Product December 31, 2019
Star Wars, Frozen 2, (Don’t F**k With) Cats…
-
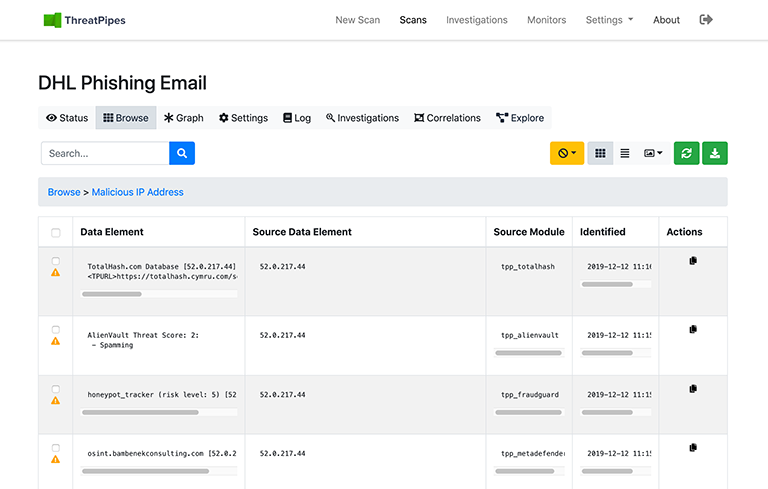
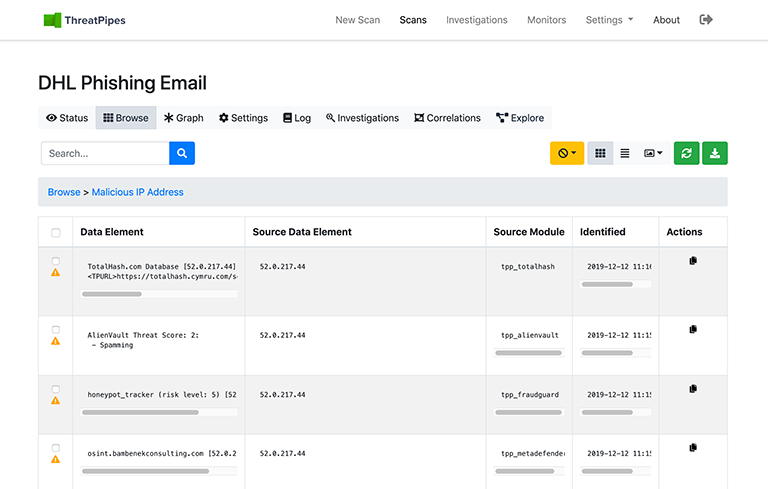
How a missed delivery ruined Christmas
Research December 24, 2019
It was the night before Christmas…
-
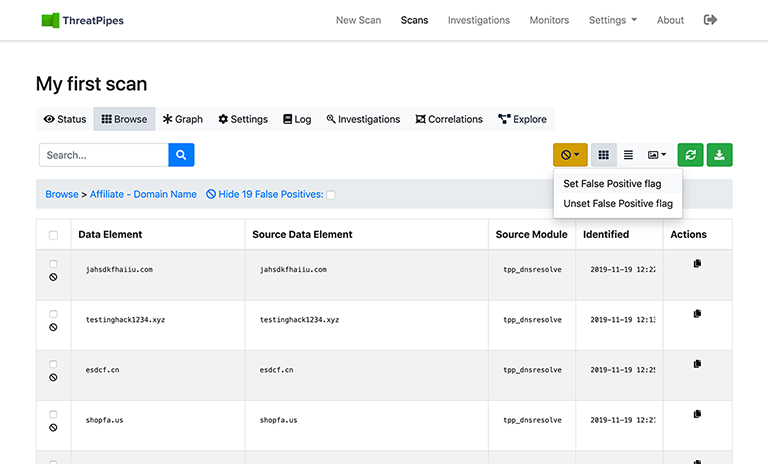
Keep your analysis focused on high-value intelligence using ThreatPipes
Product December 17, 2019
To help make it easy to filter out the noise, you can mark these results as false-positives.
-
I put my credit card on the Darkweb
Research December 10, 2019
“Are you crazy?”, you’re thinking.
-
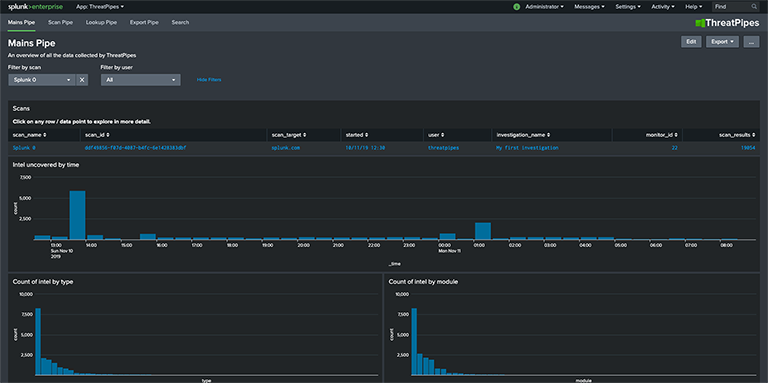
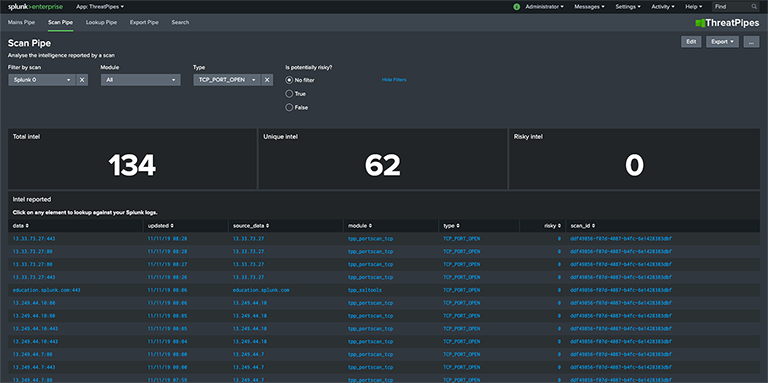
Turn Splunk into a powerful threat / vulnerability hunting tool with ThreatPipes
Product December 03, 2019
Teamed with Splunk, you can explore and examine intelligence gathered by ThreatPipes in ways never before possible.
-
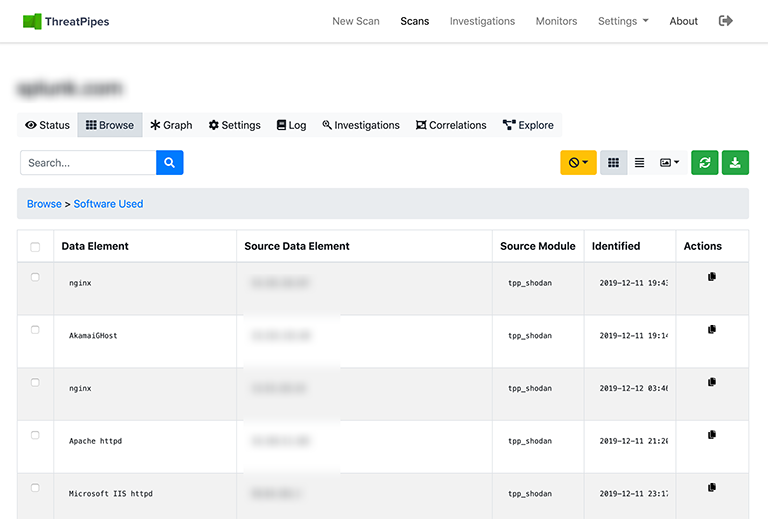
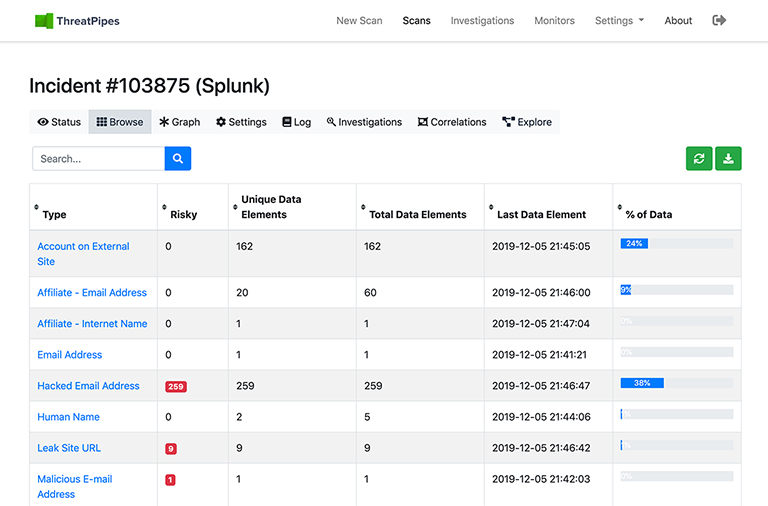
We built a Splunk App... and it found Splunk.
Research November 26, 2019
Did you lock the front door? Yes.
-
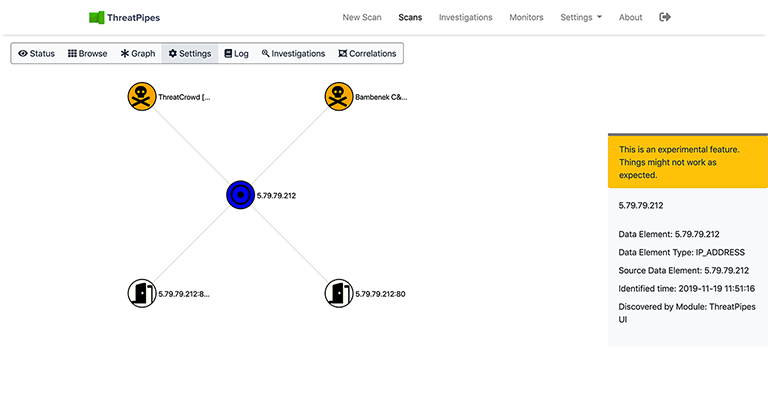
Targeted intelligence collection using ThreatPipes manual scans
Product November 19, 2019
A manual scan helps you conduct targeted intelligence gathering.
