I have 6 LinkedIn accounts.
Amy, VP of investment banking for a leading bank. 1874 connections working in financial services.
Another, Kim, working as an engineer for a top-tier technology company. 973 connections. And counting.
And the most fruitful, Sarah, Lucy and Louise. All IT recruiters. 2983 connections between them.
Oh, and of course my own LinkedIn account (with far fewer connections).
Maybe you’ve connected with one?
You squint at the obscure 100 x 100 pixel profile photo to see if you recognise them when the connection request comes in.
Did I meet them at a conference? You ask yourself.
Were they on that team I worked with once at my last company?
They look reputable. How much harm can adding them do?
Accept.
The beauty of LinkedIn (or flaw, depending on who you are) is that there is no verification. Of anything.
I can create an account, add a few past positions at any company and start connecting with people
Manager, director, VP, whoever.
You can go even deeper.
I know red teams that maintain accounts for real people who don’t have a social media presence. Those in the military often don’t. Law enforcement officers too.
Of course, scratch the surface and the truth quickly unravels. But who performs background checks on connection requests.
I thought the hardest part would be adding connections to new accounts, especially when getting started with a no other connections.
Nope. Most people simply click “Accept”.
You’ll notice all my fictitious accounts are female. There’s a reason for this. I’ve found men are much more likely to add women, than vice-versa.
Now you’re thinking; why does it all matter?
Well, I now have a platform to get in front of you.
Maybe I’ll phish you via LinkedIn messaging.
In many cases, I’ll also have access to more of your personal info. Email and phone are pretty common pieces of information people share (often unknowingly) with their connections.
Or maybe I’ll be one step closer to one of your connections that I’m targeting. Our mutual connection adds an additional level of credibility to my campaign.
Look through your existing connections. How many do you actually know?
Next time you think of hitting “accept”, ask yourself; would I share my phone number with this person?
If the answers “no”, I would ignore it.
Or at least scratch the surface of their online footprint.
ThreatPipes Modules relevant to this post
- Social Networks: Identify presence on social media networks such as LinkedIn, Twitter and others.
- Social Media Profiles: Identify the social media profiles for human names identified.
- FullContact: Gather domain and e-mail information from fullcontact.com.
- Gravatar: Retrieve user information from Gravatar API.
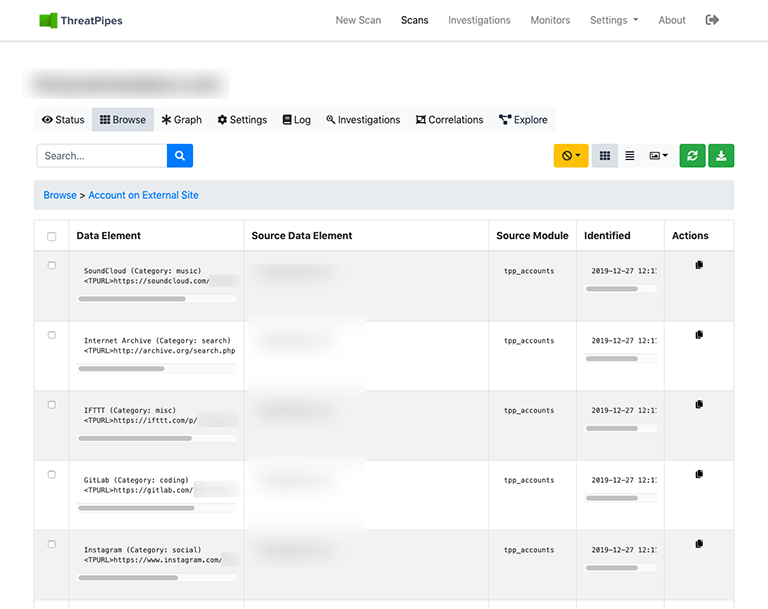
- Accounts: Look for possible associated accounts on nearly 200 websites like Ebay, Slashdot, reddit, etc.

