Would you be surprised if I told that, if you use a MiFi or WiFi tether, someone could be tracking your location?
Well… surprise!
WiGLE is a one-stop-shop for user-reported wireless network data.
Users upload information on their phones, tablets, and laptops using WiFi-sniffing tools or WiGLE’s own Android app.
I imagine you’re now checking to see if your home network has been captured.
Don’t forget about your phone.
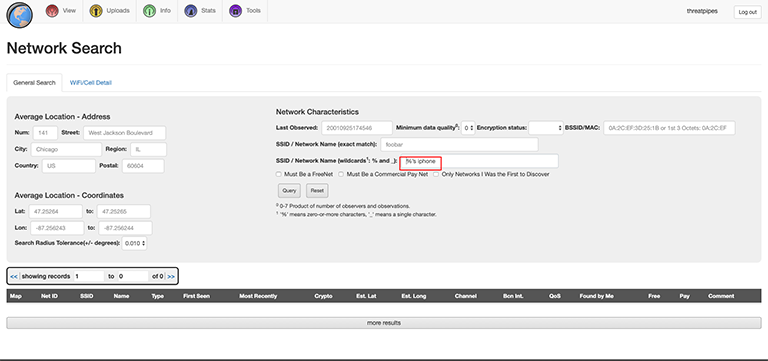
WiGLE’s advanced search feature lets you search using wildcards (e.g. %’s’ iPhone -> FIRST_NAME’s iPhone – this is the typical pattern iPhones will assign as an SSID name for the phone by default).
You can search exact matches too (if you know the BSSID/MAC address of the device).
If the device has been seen multiple times by WiGLE users, the GPS co-ordinates collected are great for tracking a persons movements.
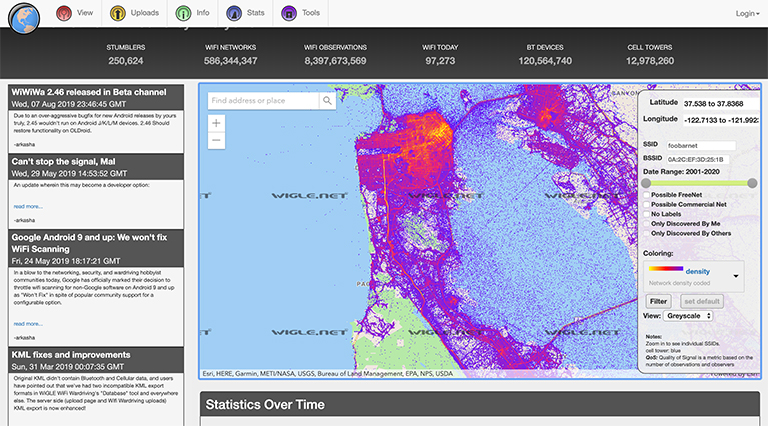
You work in London. You live in Winchester. What were you doing at that hotel?
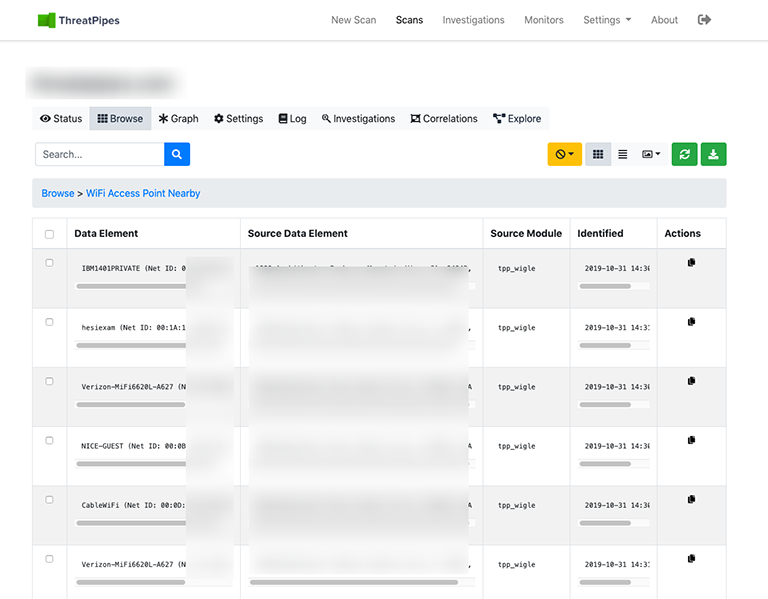
Because WiGLE publishes BSSID/MAC addresses of devices captured, it can be fun to ask clients about the devices in their office… figuring out which are easily exploitable before turning up on site.
How? The IEEE maintains the authoritative list of what MAC address (BSSID) are registered to companies.
The first 6 digits in the BSSID are the company that made the transmitter or the device. From there it’s not too difficult to find the model of the device using Google.
WiGLE deserves credit, not only for the half-a-billion WiFi data point they’ve amassed, but also for their commitment to privacy.
You can append _nomap or _optout to your SSID to ensure the network is not indexed.
WiGLE will also remove data already collected by their users if you send them an email with the BSSID of the device(s).
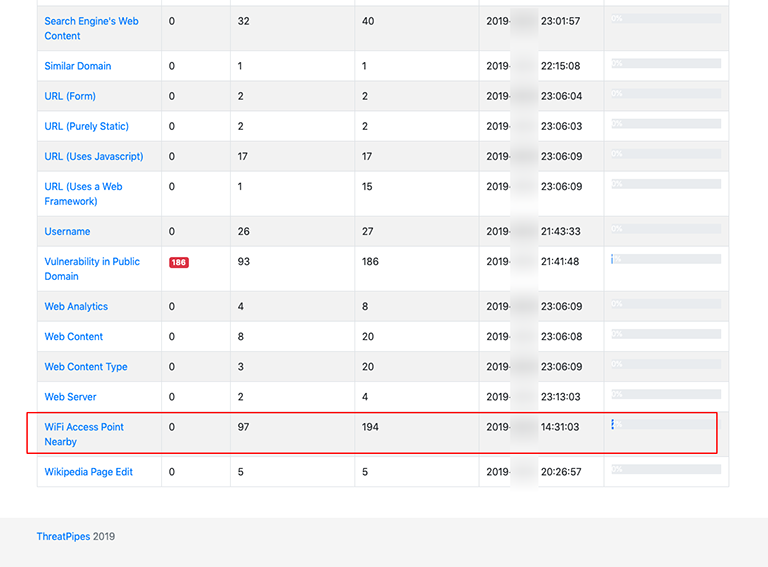
ThreatPipes Modules relevant to this post
- WiGLE: Query wigle.net to identify nearby WiFi access points.\
- Google Maps: Identifies potential physical addresses and latitude/longitude coordinates.
- OpenStreetMap: Retrieves latitude/longitude coordinates for physical addresses from OpenStreetMap API.

